Yes, send it to me.
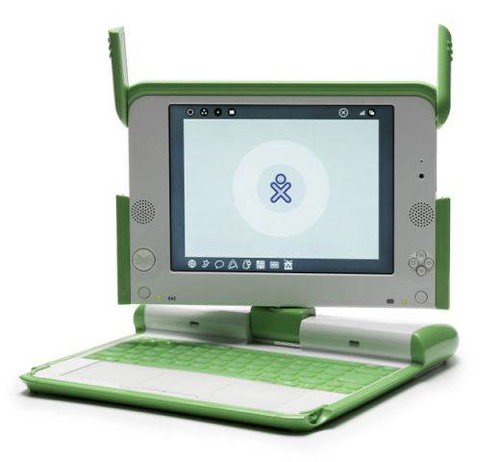
Whatever it takes right? I couldn't wait to tear into this thing.
 SSH is up and running by default out the gate. Just go to the "Neighborhood View" and connect to your in home wireless AP and you can hit ssh right away:
SSH is up and running by default out the gate. Just go to the "Neighborhood View" and connect to your in home wireless AP and you can hit ssh right away:[olpc@xo-14-7F-A0 ~]$ telnet 192.168.1.118 22
Trying 192.168.1.118...
Connected to 192.168.1.118.
Escape character is '^]'.
SSH-2.0-OpenSSH_4.5
Which is cool, but there's a catch - you can't login.
The default user is named 'olpc' - this user, as well as root DO NOT HAVE A DEFAULT PASSWORD.
The password file is shadow'd:
[olpc@xo-14-7F-A0 ~]$ egrep '^(root|olpc)' /etc/passwd
root:x:0:0:root:/root:/bin/bash
olpc:x:500:500::/home/olpc:/bin/bash
But if you look at the hash in /etc/shadow you see olpc's "current password hash" is "!!" - which is not valid:
[olpc@xo-14-7F-A0 ~]$ egrep '^(root|olpc)' /etc/shadow
root::13880:0:99999:7:::
olpc:!!:14148:0:99999:7:::
root's password is just plain empty!
Which is handy on the local system:
[olpc@xo-14-7F-A0 ~]$ whoami
olpc
[olpc@xo-14-7F-A0 ~]$ su
bash-3.2# whoami
root
But kind of awkward when you try to login via ssh:
login as: olpc
olpc@192.168.1.118's password:
Access denied
The tricky part about that invalid "!!" hash is that it's neither a blank password nor a valid password. The olpc user can't even change it's OWN password because there is NO CURRENT VALID PASSWORD:
[olpc@xo-14-7F-A0 ~]$ passwd
Changing password for user olpc.
Changing password for olpc.
(current) UNIX password:
passwd: Authentication token manipulation error
So we decide move on to root.
Root has an 'empty' password. Which is valid - but it had me raise en eyebrow as well.
login as: root
root@192.168.1.118's password:
Access denied

I was slightly forgiving after my investigation into the default configuration of OpenSSH.
bash-3.2# egrep '#Permit(Root|Empty)' /etc/ssh/sshd_config
#PermitRootLogin yes
#PermitEmptyPasswords no
Because these configuration lines are commented out, the ssh server goes with the standard OpenSSH settings. Which will NEVER allow the super user to to authenticate directly over ssh, and furthermore would not allow ANY user with an empty password to authenticate anyway.
To login to your OLPC XO Laptop via ssh you will need to:
1) open a local terminal
2) su to root
3) set a valid password for the 'olpc' user
4) connect to the laptop as the 'olpc' user via ssh using the new password you just created
e.g.
[olpc@xo-14-7F-A0 ~]$ whoami
olpc
[olpc@xo-14-7F-A0 ~]$ su
bash-3.2# passwd olpc
Changing password for user olpc.
New UNIX password:
BAD PASSWORD: it is too short
Retype new UNIX password:
passwd: all authentication tokens updated successfully.
bash-3.2# exit
exit
[olpc@xo-14-7F-A0 ~]$ ssh olpc@192.168.1.118
The authenticity of host '192.168.1.118 (192.168.1.118)' can't be established.
RSA key fingerprint is d4:5a:b0:30:0d:eb:61:9c:df:c9:32:0e:ab:ff:51:9e.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.1.118' (RSA) to the list of known hosts.
olpc@192.168.1.118's password:
[olpc@xo-14-7F-A0 ~]$
Stay tuned - More to come!

5 comments:
I believe this is on purpose, you don't want the machines to be open to ssh by default, so you must first set a password for root.
Intentional? Sure, no doubt.
Secure? Maybe...
Standard? No, not really.
I'm surprised you found this article so quickly, I just wrote it last night at like four in the morning...
Rather than set a password, you can paste in your public ssh key to /root/.ssh/authorized_keys
This allows for a secure remote access without establishing a password for any account. Someday the owner of the laptop may want to set their own passwords, it would be a shame to get in their way.
Discovering that OLPC has a default no password setup was surprising. Using qFlipper, I learned how to secure my device effectively!
Post a Comment